The digital perimeter of the modern enterprise has vanished. With the mass adoption of cloud computing, remote workforces, and the Internet of Things (IoT), securing a company’s network is no longer about building a taller firewall. Cyber threats have grown exponentially in both volume and sophistication, outpacing the capabilities of human analysts and traditional security software.
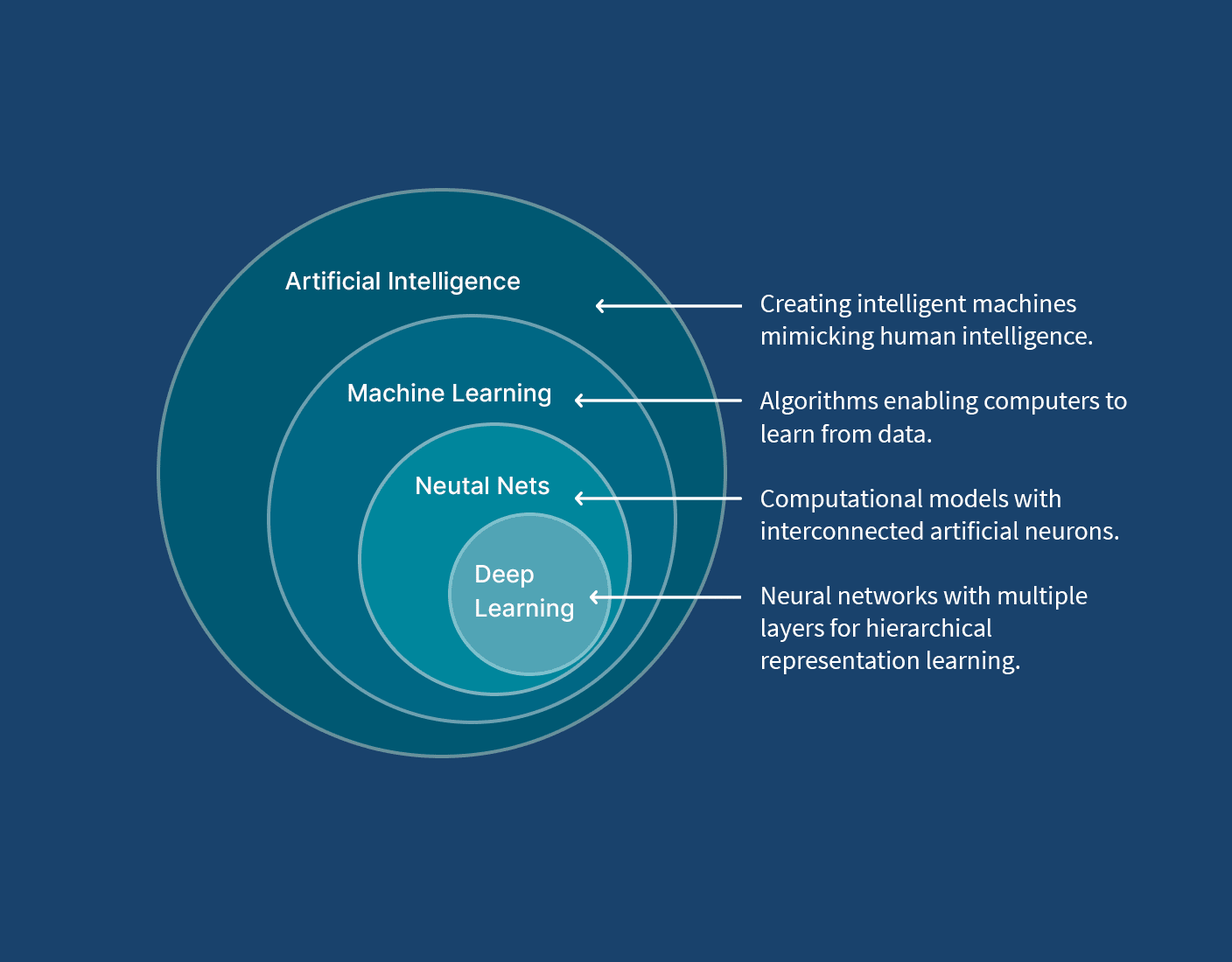
To combat this relentless wave of automated, highly targeted attacks, enterprises are turning to the very technology that is driving innovation across the globe: Machine Learning (ML). By shifting from reactive defense strategies to predictive, autonomous systems, machine learning is fundamentally rewriting the rules of enterprise cybersecurity.
The Death of Signature-Based Detection
For decades, the cornerstone of enterprise security was signature-based detection. Antivirus programs and firewalls relied on a database of known malware “signatures” or fingerprints. When a file entered the network, the security software would compare it against this database. If it found a match, the file was blocked.
The fatal flaw in this system is that it only protects against known threats. Today’s cybercriminals use polymorphic malware that constantly changes its code to evade signature-based detection. They launch zero-day attacks—exploiting vulnerabilities that software vendors don’t even know exist yet. In this landscape, traditional security is like a guard looking for a specific license plate, while the thief has already repainted the car and changed the tags.
Machine learning changes this paradigm entirely. Instead of looking for a specific signature, ML models are trained to understand what “normal” looks like on a network and flag anything that deviates from that baseline, regardless of whether it has been seen before.
The Engine of Modern Defense: Algorithms in Action
The effectiveness of machine learning in cybersecurity relies on deploying the right algorithms for specific tasks. Modern security systems utilize a blend of different ML models to create a layered defense:
Support Vector Machines (SVM):
incredibly powerful. By mapping data points in high-dimensional space, SVMs can draw distinct boundaries between benign files and malicious executables, effectively categorizing software behavior and catching altered malware that traditional systems miss.
K-Nearest Neighbors (KNN):
Network traffic is massive and chaotic. KNN algorithms are highly effective at clustering this data and identifying anomalies. If a user’s behavior suddenly shifts—for instance, an employee in the marketing department suddenly tries to download gigabytes of encrypted database files at 3:00 AM—KNN helps flag this as an outlier relative to their “nearest neighbors” (their normal historical behavior or the behavior of their peers).
Artificial Neural Networks (ANN):
Deep learning, powered by complex ANNs, is used for advanced threat hunting. These networks can process vast amounts of unstructured data, performing deep packet inspection and identifying subtle, sophisticated attack patterns hidden within encrypted traffic without needing human intervention.
Real-World Enterprise Applications
The integration of these machine learning models into enterprise environments has yielded several transformative applications.
1.Next-Generation Endpoint Detection and Response (EDR)
Laptops, smartphones, and servers are the most common entry points for attackers. Modern EDR solutions use machine learning to monitor the continuous behavior of processes running on these endpoints. If a legitimate application suddenly begins attempting to modify system registries or encrypt files (a classic sign of ransomware), the ML-powered EDR can kill the process and quarantine the device in milliseconds, long before human IT staff are even alerted.
2.Automated Incident Response and SIEM
Security Information and Event Management (SIEM) systems collect log data from across the entire enterprise. In the past, this resulted in “alert fatigue,” where security teams were overwhelmed by thousands of daily notifications. Machine learning algorithms now filter this noise. They correlate disparate events—a failed login in London followed by a successful login in Tokyo three minutes later—and escalate only the genuinely critical threats to human analysts, complete with a recommended remediation plan.
3.Advanced Phishing and Fraud Detection
Phishing remains the most successful attack vector for cybercriminals. Attackers now use AI to draft flawless, highly personalized emails. To counter this, enterprise email gateways employ Natural Language Processing (NLP)—a subset of ML—to analyze the context, urgency, and language patterns of incoming emails. Furthermore, machine learning models continuously monitor financial transactions to detect the subtle anomalies indicative of payment fraud or business email compromise (BEC).
The Double-Edged Sword: Adversarial Machine Learning
While machine learning provides a massive defensive advantage, it is not a silver bullet. The cybersecurity landscape is an endless arms race, and attackers are also weaponizing ML.
Hackers use machine learning to automate the discovery of vulnerabilities, generate mutating malware, and create hyper-realistic deepfakes for social engineering. Furthermore, enterprises face the threat of “data poisoning.” If an attacker can subtly manipulate the data used to train a company’s defensive AI, they can blind the system to specific types of attacks, essentially creating an invisible backdoor.
Defending against adversarial AI requires continuous model retraining, rigorous data validation, and a strategy that keeps a “human in the loop.” Machine learning is designed to augment human intelligence, not replace it entirely.
The Future of Enterprise Security
As we move deeper into the digital age, machine learning will no longer be an optional “premium” feature for enterprise security; it will be the absolute baseline. The speed of cyberattacks has surpassed human reaction times. Systems that can autonomously predict, detect, and neutralize threats at machine speed are the only way to safeguard sensitive data and maintain operational continuity.
For businesses, the integration of machine learning into their security posture is an investment in resilience. It represents a proactive stance in a world where the question is no longer if an attack will happen, but when—and whether the network is smart enough to stop it.